The cheese has moved again: why cyber resilience is now a business imperative
AI has industrialized cyber offense, the defensive gap is widening, and quantum computing is already on the horizon. In this new reality, preventing every breach is no longer a viable strategy. The real question is whether organizations can continue to operate while under attack. Blue Castle by Code Blue introduces a resilience-first framework designed to keep the business running when disruption is inevitable.
By: Rafael Franco, CEO and Founder of Code Blue
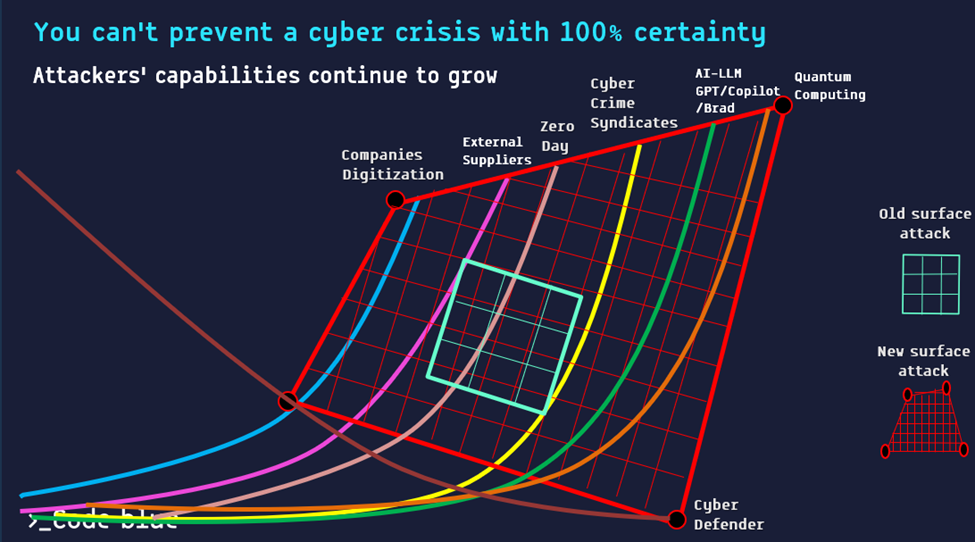
Since 2020, we have witnessed consistent acceleration in both the scale and sophistication of cyberattacks worldwide. It began with the COVID-19 outbreak, when organizations became more digital and increasingly dependent on third-party vendors. It continued with the entry of traditional crime groups into cyberspace, the expansion of zero-day exploitation and RaaS groups, and two years ago, with the industrialization of AI and its massive integration into our lives.
Now, just around the corner, quantum computing looms threatening to disrupt the encryption keys upon which decades of security architecture have been built.
The turning point: Commercial AI in 2024.
AI did not invent offensive cyber capabilities; it industrialized them and accelerated them dramatically.
On the defensive side, however, progress has been slower, more cumbersome, and still significantly behind. The bottom line: the gap is widening.
The next era: Quantum Computing.
We are expected to see substantial advances in applied quantum capabilities between 2026 and 2028, including improved qubit stabilization and computational scaling.
Full operational maturity may still be years away, but the preparation window is narrowing and already visible.
The world is shifting from Cyber Security to Cyber Resilience.
Resilience First – A Paradigm Shift
The Resilience Framework developed by Code Blue is not merely another technological control layer. It is a conceptual ecosystem designed to enable an organization to manage itself during a cyberattack.
At its core, it represents a shift:
- From preventing intrusion to managing operations under attack.
- From technical response to coordinated organizational management.
- From the assumption “we will block everything” to the understanding that breach is a baseline scenario.
- From excessive risk avoidance to structured risk management.
- From focusing solely on defense to focusing on functional continuity.
The real question is not whether an attack will occur, nor whether the organization will fully block it.
The question is whether the organization can continue to function during a cyberattack, repel it, and return to normal operations.
Blue Castle by Code Blue embodies the resilience concept end-to-end. It enables organizations to manage continuous exposure to attacks and incidents, maintain ongoing regulatory and operational readiness, and make informed decisions under uncertainty and crisis conditions, while protecting business continuity and reputation.
Built on a holistic CIRM approach, Blue Castle by Code Blue operationalizes resilience across the enterprise.
In conclusion
The global technological reality demands the adoption of a new operational paradigm: Code Blue’s Resilience Framework and the Blue Castle platform. Organizations that fail to adapt their defense philosophy will, unfortunately, learn this the hard way.
Do you have questions or want to learn more?
Contact Us
Founder and CEO of Code Blue, international expert in cybersecurity and crisis management. Former Deputy Head of the National Cyber Directorate and Head of the Defense and Operations Division. Author of the book PLAN B.
Related Posts

La piattaforma TPCRM di Code Blue supporta le organizzazioni nella gestione strutturata e continua del rischio cyber dei fornitori lungo l’intero ciclo di vita. Combina automazione avanzata e AI per monitoraggio costante, compliance a NIS2, DORA e GDPR e protezione dei dati, garantendo controllo, tracciabilità e resilienza in un contesto di rischio crescente.
